Firewall under fire

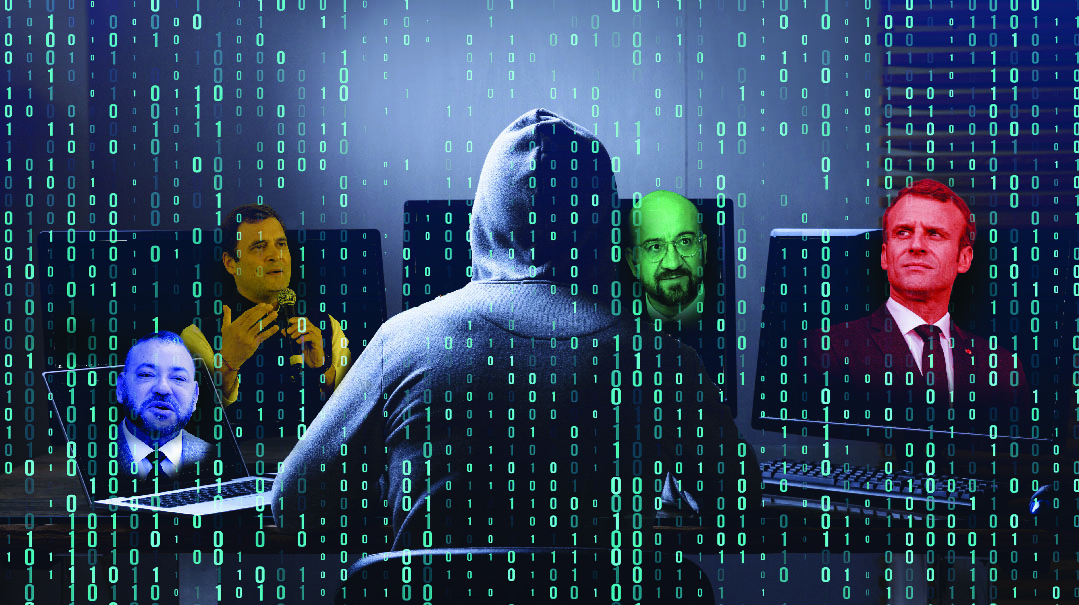
As Israeli-made offensive cyber-tech from the NSO Group is revealed to have targeted world leaders, will Israel’s own edge be blunted by foreign-sales restrictions?
"Many allies spy on each other,” it’s been said. “the trick is not to get caught.”
Having indirectly broken that cardinal rule after Israeli-made technology targeted Western leaders such as French president Emmanuel Macron, Israel’s new leadership finds itself under pressure to rein in the country’s private surveillance-tech outfits.
A long-running joint investigation by the Guardian and Washington Post broke the story last week that NSO Group Technologies, a Herzliya-based company whose spyware tool called Pegasus allows the remote penetration of smartphones, had provided the know-how that was used to listen in on a slew of world leaders, journalists, and opposition figures.
That list includes Macron, WHO director-general Tedros Adhanom Ghebreyesus, South African president Cyril Ramaphosa, Lebanese prime minister Saad Al-Hariri, European Council president Charles Michel, Kind Muhammad VI of Morocco, and a host of others.
But while the story is turning up the diplomatic heat on new prime minister Naftali Bennett, the episode also shines a light on an entire ecosystem of offensive cyber-tech.
If Israel has produced a Mobileye in transport technology, that’s because multiple companies are working on the same project; in the same way, NSO testifies to a widespread project parlaying the country’s spy tools into for-export use. By nature of an industry closely linked to Israel’s intelligence world, “no comment” is the standard response. But conversations with multiple sources in the defense establishment built up a picture of NSO’s operating environment.
Industry insiders call NSO Group “Unit 8200 on steroids,” referring to the IDF’s famed signals-intelligence unit. The question is if, in light of these revelations, the steroid level might have to be turned down, or will Israel brush off the attacks as just another embarrassing report from left-wing-oriented media outlets.
A Flying Trojan Horse
The NSO Group (the initials stand for the first names of the firm’s founders, Niv Carmi, Shalev Hulio, and Omri Lavie) was founded in 2010 in Herzliya, and now employs some 600 people. The founders are former members of the IDF’s elite Unit 8200, which is famed for its abilities to gather intelligence through communications surveillance.
The company’s Pegasus application is Trojan horse malware covertly installed on smartphones that spies on all of a user’s communications, without his awareness. The company insists it sells Pegasus only to foreign governments.
As a cyber developer, NSO Group’s contracts with foreign powers have to be approved by Israel’s Defense Export Control Agency (DECA). Despite this, past reports show that Pegasus has reached the wrong hands more than once.
NSO Group is only one example. Many other companies work in the same field but maintain a lower profile. Information obtained by Mishpacha showed that there’s a wide commercial cyber weapons market that exports products almost everywhere, and Israel’s regulatory process is far from transparent. The current episode has raised a big question mark around regulation of cyber exports, a topic that doesn’t receive much publicity in Israel.
These companies employ Israel’s best and brightest. They are formed, maintained, and staffed by Israel’s best tech experts, most of them veterans of elite IDF units. A security official we spoke with speculated that this may be where the problem lies. The transition from the army, with that framework’s sense of mission, to the private sector, with its wealth of opportunities — not all of them honest — is problematic from a moral perspective. Some of these men and women, according to private conversations, view themselves as real heroes, imposing a new world order and deciding who are the good guys and who are the bad guys.
NSO Group doesn’t talk much about its products. What is known is that the company has developed a product with no equal in the world: Pegasus allows a hacker to extract any information from a mobile device, including texts, pictures, and recordings without leaving any tracks behind, and to remotely activate the phone’s camera and microphone at any time. Naturally, the product is much sought-after by governments and intelligence agencies.
Countries like Israel and the US have the ability to develop powerful surveillance tools of their own, and have probably done so. But many other countries don’t have this capability, and have to turn to NSO. Before they can buy the spyware, the Israeli government has to approve the purchase, and it’s sold exclusively to governments and not to individuals or private companies. Nevertheless, more and more accusations have surfaced that Pegasus is used by some governments to crack down on political dissidents, not terrorists or dangerous criminals as the company claims.
The CEO and co-founder of NSO Group, Shalev Hulio, in an attempt at damage control, told Yisrael Hayom this week, “We’ll be very happy if the affair is investigated so we can retain our good name. We never had and don’t have any connection to the list [of world figures] that was publicized, and if it turns out that one of our customers misused our program to track journalists or human rights activists, the contract will be terminated immediately. We’ve proved this in the past, including with some of the biggest customers we’ve worked with.”
Hulio repeated that NSO sells only to governments, not companies or private individuals; and won’t sell it to just any government, such tools shouldn’t all into the wrong hands. “With a perspective of 11 years since the company’s founding, we have 45 companies and 90 countries that we’ve turned down,” he said.
He also stressed that NSO Group does not operate the system itself. “We give the necessary instructions and leave our customers to their own devices.”
He concluded, “We want to be under regulatory supervision of [Israel’s] Defense Ministry. We’ve been supervised on our initiative since 2010. We never concluded a single contract that wasn’t supervised.”
Asked who could have perpetrated the criminal acts that drew world headlines last week, Hulio speculated that it was a “hidden hand, perhaps Qatar, the BDS movement, or both, channeling the exclusive focus on Israeli offensive cyber technology. Some people don’t want ice cream to come here, or our tech to be exported.”
Israeli media such as left-of-center Calcalist took issue with this assertion, noting that it played on patriotism to deflect the real ethical questions raised. But they also pointed out that the focus on Israeli tech comes from groups like Amnesty Internationl, who have a bad track record in this regard. Furthermore, they pointed out that the US itself sold weaponry to states like Turkey and Saudi Arabia, who have used them to their own ends. Israel, in other words, shouldn’t be held to a higher standard.
Spyware Start-Ups
All Israeli companies active in spyware and surveillance have to receive a license from DECA. This can be a long and tortuous process. In 2016, NSO Group was the first to start talks with Saudi Arabia about selling weapons systems to the country. Even these negotiations required authorization from the Defense Ministry, and this was given.
The Saudis made contact with at least three other Israeli companies, Quadrim, Candiru, and Verint, all three of which received licenses from the Defense Ministry to do business in the kingdom. Cellebrite, which manufactures phone hacking technologies, also sold its services to the Saudis, though without DECA’s approval, Ha’aretz reported. Another company called Netline has done business in other countries, most notably Mexico.
Vernit develops IMSI-catchers, a tactical cyber weapon which acts as a cell tower and thus connects to mobile phones. The hack enables tracking the precise location of mobile phones as well as intercepting calls and data.
Netline sells communication jammers that can block communication in a prison, for instance, to prevent inmates from using smuggled devices. Cellebrite sells a product called UFED, Universal Forensic Extraction Device, which can bypass passwords to access data from a locked mobile device, a tool used by police forces across the world.
Candiru specializes in hacking Windows systems. Last week, Microsoft publicized details about the weaknesses of its operating system, through which the company claimed Candiru could hack computers. Microsoft accused Candiru of helping its governmental clients spy on journalists, politicians, dissidents, and human rights defenders across the world. Candiru sold at least one system to Saudi Arabia, and in May 2018 an intensive negotiation began between the kingdom and the company.
Conversations with forces familiar with the subject showed that a number of cyber weapon systems used by different companies stopped working after the weaknesses they exploited were blocked. At least one system is still operational and is used by Saudi intelligence.
A source from Israel’s Defense Ministry said this week that the Israeli cyber weapon industry sells equipment to pro-Western countries such as India and Saudi Arabia, to avoid harm to Israel’s strategic interests. If Israel doesn’t sell to them, then American, Cypriot, Russian, Chinese, and Italian companies will take their place, and likely won’t draw the press coverage that Israel gets.
“Who supplies the Iranians with Trojan horses?” asked the source rhetorically. “Where do Russia’s cyber weapons come from? Or China’s? Who sold Hezbollah eavesdropping technologies that allowed them to catch pro-Israeli spies?”
According to the Defense Ministry source, if Israel didn’t sell cyber programs to pro-Western countries, the interests of Israel and the West would be vulnerable to attacks from North Korea, Russia, China, and Iran. For this critical industry to be able to function and grow, Israeli firms have to sell their products to countries with similar interests, even if they’re dictatorships.
The Defense Ministry issued a formal statement to the effect that it supervises and inspects the export of cyber weapons while adhering to international standards “and even exceeding them.” Per the statement: “In every decision, we take into account a wide array of considerations including security, diplomacy, and strategy, all while adhering to international human rights agreements.”
The Defense Ministry’s supervision doesn’t stop when a license is issued. “We continue monitoring companies and when necessary, if it’s found that use was made contrary to the terms of the license, steps are taken to cancel the company’s export license.”
Unwanted Scrutiny
The NSO Group story suddenly burst onto front pages when French president Emmanuel Macron called Israeli prime minister Naftali Bennett directly on the phone last Thursday to demand answers as to why his phone had been tapped using Pegasus.
Macron’s name is one in a long list of politicians and journalists around the world whose mobile devices were apparently infected with the spyware. The list includes ten current and former prime ministers, three presidents, a former president, and a king.
Macron was unnerved to learn that his mobile phone, as well as those of several of his cabinet members, had been exposed to spyware designed to collect information about them. In his conversation with Bennett, Macron made clear that France wants to know whether Israel plans to investigate NSO, whether the surveillance materials reached foreign hands and if so, whose, and whether Israel will step up its supervision of the export of cyber weapons. In addition, the French government wants reassurances that Israel will take action against NSO if it becomes clear that it violated the terms of its export license.
According to reports in the world press, Bennett promised Macron that Israel would open an investigation into the alleged misuse of the spyware for surveillance of politicians, political dissidents, and activists. At the same time, the prime minister emphasized that even if the spying did take place, it happened before his time, under the watch of Binyamin Netanyahu.
France isn’t the only country to express concern regarding the reports about the Israeli company. According to various reports, figures in the American administration have made clear to Israeli security officials that the episode could have repercussions for future defensive pacts. The American administration won’t quickly forgive anyone involved even indirectly in the incident, they said repeatedly.
Whatever the repercussions for Israel’s relations with foreign governments, the country’s cyber tech industry will likely be forced into a more cautious posture moving forward, in many ways a victim of its own successes.
(Originally featured in Mishpacha, Issue 871)
Oops! We could not locate your form.













